TLDR
- David Schwartz said KelpDAO may have skipped key LayerZero security features.
- LayerZero said the April 18 exploit cost KelpDAO about $290 million.
- Schwartz said bridge teams often promote easy setups over stronger safeguards.
- He said simple bridge models can grow before stronger controls are added.
- LayerZero linked the attack to a likely DPRK state actor in early findings.
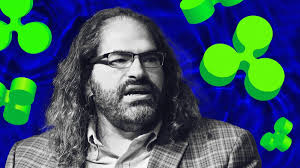
Ripple CTO David Schwartz said KelpDAO may have skipped key bridge safeguards before its recent exploit. He made the remarks while discussing bridge security choices and LayerZero’s setup model.
Schwartz said he reviewed many DeFi bridge systems for RLUSD with a focus on risk and security. He said many systems offered strong protections, yet projects were often guided toward easier setups with lower operational costs.
Schwartz points to bridge security trade-offs
Schwartz said many bridge providers promoted strong security features during discussions with potential users. However, he said those same systems were often sold on the ease of adding chains without using the strongest controls.
He wrote that most schemes were well designed and included protections against the type of attack seen in the KelpDAO case. Still, he said teams were often encouraged to avoid the most important safeguards because they created more work.
In one post, Schwartz said, ”Their sales pitch was that they have the best security features but they’re easy to use and scale assuming you don’t use the security features.” He added that this pattern appeared often in DeFi bridging.
He also said, ”I have a funny feeling part of the problem is going to be something like KelpDAO choosing not to use key LayerZero security features out of convenience.” He said he hoped that view would prove wrong.
LayerZero statement adds detail to the attack
LayerZero later published a statement on the KelpDAO incident. The company said KelpDAO was exploited on April 18, 2026, for about $290 million.
The statement said early signs pointed to a highly sophisticated state actor. It added that the likely source was DPRK’s Lazarus Group, based on preliminary findings.
After that statement, Schwartz posted again and said the attack appeared more advanced than he first expected. He wrote that the exploit was aimed at LayerZero infrastructure and used what he called KelpDAO laziness.
He said, ”The attack was way more sophisticated than I expected and aimed at LayerZero infrastructure taking advantage of KelpDAO laziness.” His comment tied the breach to both attacker skill and setup choices.
Debate grows over who controls bridge safety
The discussion also turned to how much freedom projects should have when choosing security settings. Some users argued that letting applications choose their own model creates a race to weaker protection.
Schwartz said simple setups can make sense in limited cases. He said they may work when value is low, or when bridges serve private ledgers and backed assets with a trusted party.
Still, he said problems begin when those temporary choices remain in place as larger sums move through a bridge. He wrote that teams often say they will improve security later, but those changes may never happen.
Schwartz also said governance remains a hard issue in decentralized finance. He said no one has fully solved decentralized governance when decisions affect who gets money. That point added another layer to the wider bridge security debate now surrounding KelpDAO, LayerZero, and future stablecoin integrations such as RLUSD.